Simply put, cyber espionage is a type of an attack in which an unauthorized user views and accesses otherwise classified information. Cyber espionage often includes very subtle practices – often nothing more than a few lines of code running in the background of a mainframe, targeting mainly corporate or governmental entities.
Obviously, the goal of these attacks is not simple curiosity, but rather the obtainment of business secrets or intellectual property. The motivation behind them is usually greed and financial profit. However, when these practices combine with military operations, they constitute a form of terrorism.
The consequences of cyber espionage can be dire – ranging from financial or material losses, company infrastructure, data or even death.
Common Cyber Espionage Tactics
Spies and spying are hardly a new phenomenon. However, gone are the days of tuxedo-wearing, gentleman spies, casually sipping their shaken, not stirred martini. The spies of today, generally, rely on tech and utilize cyber warfare techniques in order to achieve their goals – such as damaging governmental, business or military infrastructure or accessing financial systems.
Cyber spies most frequently target:
- Internal data,
- Intellectual property,
- Client and customer data, and,
- Competitive intelligence.
They are quite capable of creating chaos on a global level. They can disrupt international events, or even change election outcomes. And, because they are able to cover their tracks so well, most of these criminals cannot be trace for years. In turn, this invisibility has further emboldened spies to branch out to other industries, targeting even public administration, manufacturing and education.
Cyber espionage prevention is now the buzzword on everyone’s lips – coming from the private and public sector, small companies and large corporations.
They say that market competition is a healthy drive for growth. But one of its consequences is that companies have been trying for decades to score an advantage over their competitors by trying to access their business plans and secrets.
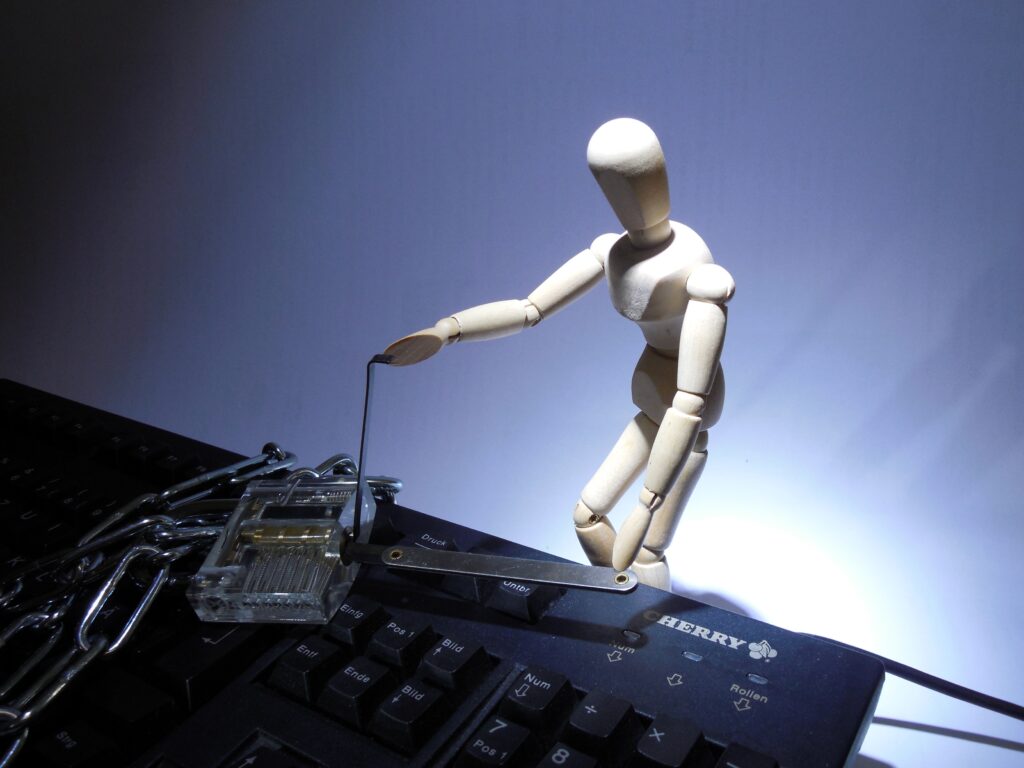
An especially popular and effective tactic has been using, so-called, imposter employees to obtain insights into their competitors’ projects. Another popular approach is relates to exploiting unattended devices. A criminal can simply insert a USB stick and upload malware by using these unsecured workstations in order to identify an open security portal or other exploit.
Company websites tend be open to these types of risks and experienced hackers know how to identify vulnerable websites in order to attack them. Sometimes, important employees receive official-looking emails. They are lured into clicking on suspicious links and downloading code that can be used for later attacks.
Recent Cyber Espionage Attacks
Back in 2009, Google noticed a trend of cyber-attacks targeting user information specific to Gmail accounts. This problem was later code-named Aurora. More than 20 companies – apart from Google, were targets of a particular vulnerability in the Internet Explorer.
Hackers used those targeted emails to distribute malware to individuals they thought had access to valuable intellectual properties. Similar acts of cyber espionage are still very common, even though attack methods have grown more sophisticated.
Chinese and Iranian Hacker Attack on US Agencies
In 2019, the United States revealed a series of attacks by hackers from Iran and China on governmental agencies and US businesses. Experts believe that these attacks are a consequence of Trump’s decision to withdraw from a nuclear deal with Iran and his countries trade war with China.
US intelligence experts linked China, Iran, North Korea, and Russia with cyber espionage activities of stealing information and influencing its citizens in order to damage critical infrastructure in the country as well as position themselves for future cyber-attacks.
Pakistan’s Foreign Affairs Ministry Website Attack
In the same year, the website of the Pakistan’s Ministry of External Affairs was the target of an attack, creating issues for any person that tried to access it outside of Pakistan – while functioning normally inside the country. This attack was linked to a group of hackers from India. Supposedly it came as a consequence of a terrorist strike in Kashmir earlier that year.
And this was not the first time that Pakistan experienced these issues. In 2017, a political party’s website was a target of an attack, as well as the portal of the Karachi police. Hackers from India were behind both of these attacks, pressumably.
The Slingshot Report
In 2018, Kaspersky Lab, a global cyber security company, exposed the activities of an APT actor, internally named “Slingshot”. Most of their victims included African and Middle Eastern countries, with first attack occurring way back in 2012.
Reportedly, Slingshots goal was to collect network and keyboard data, as well as screenshots, passwords, USB connections etc. After the report, former US intelligence officials suggested that Slingshot was a US military program designed to access terrorist’s computers.
The Take-Away
For most people, the world of cyber espionage represents a distant concept, without real importance. To the average citizen, its potential harm is not something they will feel in their every-day life. Ironically, its effects on a macro scale are more significant.
Cyber espionage results with stolen data, the loss of personal information and damaged reputations. When targeting government agencies, it can also result in loss of life due to the leaked information.
Even though loss of data and life is usually the primary concern, damages done to reputation can also have very adverse effects. If a company finds itself in a situation where its infrastructure was used to enable cyber espionage, its relation with its clients and shareholders is also at risk.
Sadly, there is no way of completely eliminating the possibility of these attacks. That is why companies and other organizations need to carefully asses their current security, evaluate risks and put forward policies that will help them fix those issues.
Organizations need to follow, record and verify their software and hardware updates, backups and have device management policies.
Also, employees are the first line of defense and its weakest link. That is why adequate education of potential security risks and best practices is vital. Once employees realize the potential for damage, they are much more likely to follow company security policies.