Protest activity has always been an effective force for social change, often challenging the status quo and raising awareness for a wide range of issues. It has also been destructive when peaceful assembly moves into confrontational gatherings.
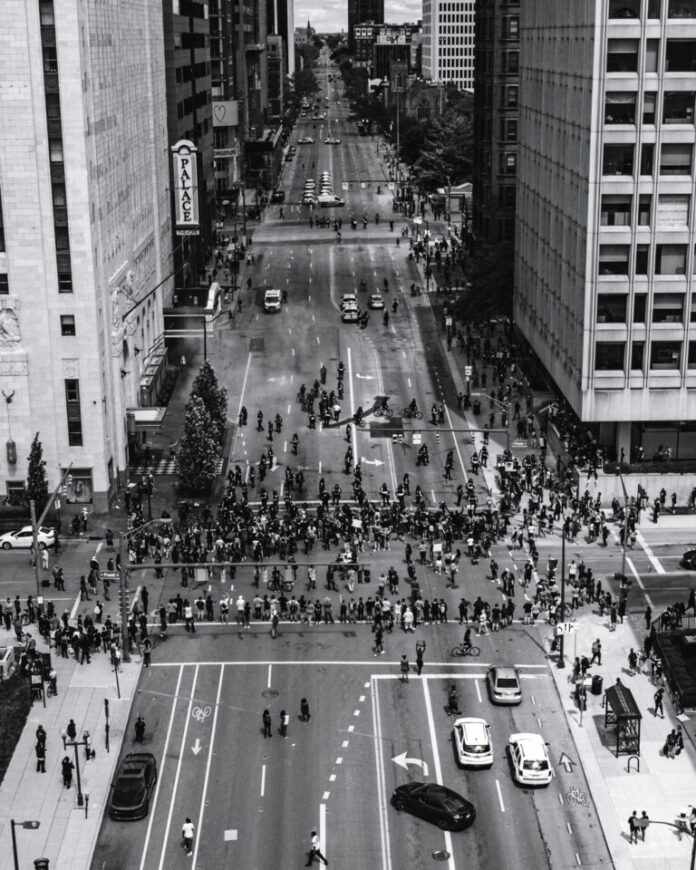
In recent years, U.S. corporations have increasingly found themselves as the targets of negative protest activity seeking a response to the demands and concerns raised by protesters. Protest activities worldwide have demonstrated increased sophistication in tactics and organizational capabilities and have evolved to leverage technology, social media, and strategic planning to amplify their messaging and achieve their objectives. This article will examine various groups, tactics, and responses to highlight the growing sophistication of protest activity and the influence it has on corporations.
To prepare for protester activity, corporate security leaders must first understand the types of protests that can be leveraged against their companies when developing plans to counter or manage the activity. It is important to recognize that protest types often fall into many groupings despite their centralized theme and motivation.
Protest Types
Boycotts and Demonstrations
A common form of protest activity is centered on organized boycotts and demonstrations, which allow protesters to voice their grievances. In recent years, there have been boycotts and protests against companies like Nike, Amazon, and Nestlé due to concerns related to labor practices, environmental impact, or alleged unethical behavior. Extinction Rebellion (XR) has gained recent attention for its disruptive protest tactics aimed at raising awareness for climate change.
Using methods such as road blockades, mass arrests, aircraft vandalism, and public demonstrations, XR has disrupted company operations in several major international cities. The group’s strategic planning, non-violent civil disobedience, and ability to generate media coverage have shown effectiveness in garnering fringe public support. The Pro-Democracy movement in Hong Kong is another effective protest group that has displayed remarkable tactical adaptability in response to heavy government restrictions.
Protesters have employed a decentralized organizational model, encrypted messaging apps, and creative strategies to outmaneuver authorities. Their use of flash mobs, human chains, and innovative communication methods and coordination has challenged traditional security measures and posed unique tests for law enforcement responses.
Divestment Campaigns
Another financially centered protest activity advocates for divestment from companies involved in controversial industries or practices. For example, protest campaigns against fossil fuel companies have called on universities, pension funds, and other fiscally centered institutions to divest from fossil fuel-related investments by pressuring these corporations to address climate change concerns.
More recent protests at major universities have also centered on the Israeli conflict, foreign financial associations, and perceived national support of public policies. The Yellow Vest movement in France highlights the challenges posed by social fragmentation in protest activity which has become commonplace within modern protest groups. Initially sparked by fuel price hikes, the movement expanded its protest activity to encompass broader socioeconomic grievances and divestment demands.
Its lack of centralized leadership and the diverse ideological backgrounds of its members have made it challenging for authorities to engage in constructive dialogue and address the underlying protester concerns effectively. Currently, these divestment campaigns range widely from conservative media campaigns to geo-political anti-Russian messaging.
Supply Chain Activism
Activists may target corporations with social campaigns focused specifically on their supply chains. This includes advocating for fair labor practices, product sourcing and improved working conditions in factories or farms that supply goods to multinational corporations.
The “Sweatshop-Free” movement is one example of this type of activism. Supply chain activism can be used to overload existing corporate processes and includes cyber hacktivist activity as one of the many tools used by protesters to disrupt corporate operations. Cyber attacks have the ability to cause large economic losses and damage to corporate infrastructure. “FloodNet” software tools have been used by protest groups for virtual sit-ins by overloading corporate websites with e-mails and crashing e-commerce sites. Most recently, the goal of cyber protestors and hacktivists has been to intentionally destroy networks and data, rather than bring public attention to or embarrass corporations.
Environmental Activism
Protesters often target corporations involved in industries perceived as harmful to the environment. This can include protests against companies in the fossil fuel, deforestation, or chemical manufacturing sectors. For instance, protests against oil and gas companies seeking to develop new pipelines or extract fossil fuels in new areas and with new means have gained significant attention in recent years.
The Sunrise Movement, a youth-led organization focused on climate activism, is one such group and has effectively protested against companies like ExxonMobil, JPMorgan Chase, and BlackRock, demanding divestment from fossil fuels, transitioning to renewable energy, and holding corporations accountable for their environmental impact.
The Rainforest Action Network (RAN) has targeted private corporations involved in deforestation and perceived negative environmental practices. RAN has protested against companies like Chevron, Bank of America, and JPMorgan Chase, calling for an end to financing activities contributing to rainforest destruction and climate change.
Human Rights Concerns
American corporations operating in other countries that follow dissimilar human rights practices may face protests calling for improved labor conditions, fair wages, or an end to complicity with oppressive governmental regimes. Companies operating in industries such as technology, apparel, or natural resource mining routinely face criticism and protests centered on human rights concerns.
Human rights protest activities are not limited to foreign operating companies but also occur in the United States. The Fight for $15 movement is an American organization that coordinates protests and strikes across the United States to demand a $15 minimum wage. They have targeted fast-food chains like McDonald’s, Wendy’s, and Burger King, highlighting income inequality and advocating for fair wages and better working conditions in the fast-food industry.
Animal Rights Concerns
Animal rights organizations and grassroots activists often play a significant role in organizing and coordinating successful campaigns using tactics such as peaceful demonstrations, public awareness campaigns, and online activism to advance their cause.
The Blackfish protest campaign targeting the use of marine mammals at SeaWorld is probably the most prominent animal rights protest activity in recent years, however, Fur Industry Protests, Animal Testing Campaigns, Factory Farming, Animal Transport Protests, and Animal Entertainment Industry Protests are continuous across all government and private industry sectors.
Globalization and Trade
Often associated with activity surrounding G8 meetings and the World Bank, protests against free trade agreements, globalization policies, and their impact on local economies and jobs often draw large crowds of civilly disobedient protesters that may impact the security of company leadership, key facilities or company assets.
Groups like the Global Justice Movement have historically protested against the G8 and World Bank, among other international institutions. Groups in this category also include Anti-Globalization Activists, Environmental Organizations, Human Rights and Social Justice Advocates, Anarchists, and Indigenous Rights Groups.
Online Activism
With the increase in digital device use and socially engineered online marketing campaigns, online activism has become an effective protest tool. The goal of these groups is to use digital tools to raise awareness, organize action, and exert pressure on individuals or organizations.
Online activists often use online petitions, social media campaigns, hashtag activism, and online fundraising for their causes. The #MeToo movement, which targeted internet and social censorship, is probably the most effective and best-known online activism campaign.
Social Justice and Equality
Private corporations routinely face protests related to social justice issues. Protests against perceived discriminatory practices, lack of diversity in hiring, or unequal pay initiatives have targeted companies across various industries, including technology, finance, and entertainment.
United Students Against Sweatshops (USAS) is a student-led organization that has protested against several private companies over labor conditions and workers’ rights. USAS has targeted clothing numerous manufacturers advocating for fair wages, safe working conditions, and the right to unionize for workers in the global apparel industry.
Corporate Optics and Business Response Considerations
Public Perception and Reputation
The primary purpose of protest activity is to impact a corporation’s public perception, reputation, and bottom line. In the era of social media and instant information sharing, protests can quickly gain widespread attention, potentially amplifying negative sentiment or highlighting perceived ethical or social issues associated with a company’s business practices.
The socially centered divestment campaign against Bud Light is a powerful example of the significant effectiveness of reputational damage linked directly to protests. This public scrutiny can influence corporate decision-making as companies seek to protect their brand image, respond to stakeholder concerns, and maintain public trust.
Consumer Activism and Market Dynamics
Protests may reflect the sentiments and demands of consumers, who are increasingly demanding ethical, sustainable, and socially responsible best practices from the companies they support and purchase from.
Consumer activism can influence corporate decision-making by pressuring companies to align their values and operations with the expectations of their target market. In response, corporations may adjust their product offerings, sourcing practices, or corporate policies to meet evolving consumer demands and maintain market superiority.
Stakeholder Engagement and Investor Relations
Protest activity can prompt corporations to communicate and engage with their stakeholders more actively. Protests may draw the attention of investors, shareholders, and other stakeholders who may seek transparency and accountability from companies.
To address concerns raised by protest movements, corporations may need to establish dialogues, conduct stakeholder consultations, or adopt policies that demonstrate their commitment to sought-after business practices. Engaging with stakeholders can help inform corporate decision-making and help build trust and long-term relationships.
Regulatory and Legal Considerations
In some instances, protesters seek the attention of government agencies to influence corporate decision-making through regulatory and legal responses. The goal is to draw attention to perceived corporate inequity and influence the oversight or revision of regulations that impact specific industries or business practices.
Corporations are then forced to navigate these changing regulatory landscapes, ensuring compliance, and adapting their strategies and operations accordingly. Legal considerations, such as potential liabilities or reputational risks, can also influence corporate decision-making in response to protest activity.
Employee Engagement and Internal Corporate Culture
Protest movements sometimes resonate with company employees, who may have concerns with corporate practices or social issues. To maintain a positive work environment and retain talented employees, corporations may need to address these concerns and foster an inclusive and supportive culture.
Listening to employee feedback or supporting social causes can be part of a proactive corporate response to protest activity, shaping corporate decision-making to align with employee expectations.
Protester Rights
When developing a security response to protest activity, corporate leaders should understand the legal implications and remedies that may follow. Protest activity in the United States is protected by several U.S. laws and long-established legal principles. Most countries outside of the U.S. have similar laws that follow the same principles. The statement “Your rights end where mine begin” is the common foundation for the legal rights of all stakeholders involved in protest activity.
Corporate security leaders must understand that while the Bill of Rights protects “peaceful” protest activities, the legal protection afforded to protesters is not absolute. Restrictions on time, place, and manner of protests may be legally imposed to ensure public safety, prevent disruption, or balance competing interests. Additionally, the specific interpretation and application of these rights may vary in different legal contexts, subject to judicial review and evolving legal standards.
It’s important to recognize that companies and their employees have the same rights as protesters with the additional rights of property ownership. Coordinating with local law enforcement and pre-protest planning is essential in developing strategies to limit the negative impact of protest activity while maintaining uninterrupted business continuity.
The First Amendment of the U.S. Constitution guarantees the right to freedom of speech, encompassing verbal, written, symbolic, and expressive forms of communication. Protesters have the expressed right to peacefully communicate their views, voice dissent, and engage in political discourse during protests.
The First Amendment also protects the right to peacefully assemble. This includes the right to gather in public spaces, such as parks or sidewalks, for the purpose of expressing collective opinions, advocating for causes, and engaging in peaceful protest activities. Protesters do not have the right to physically impede others or protest on private property without approval. Security teams should interact early and often with local law enforcement to ensure timely responses to protest activity are appropriate based on the needs of the company and in the best interest of public safety for all parties.
In addition to personal rights, the First Amendment protects the freedom of the press, which allows journalists and media organizations to cover and report on protest activities. This ensures that protest events are documented and disseminated to the public, facilitating transparency and accountability.
The First Amendment also guarantees the right to petition the government for redress of grievances. Protesters have the right to present their concerns or demands to government officials and seek changes in policies, laws, or regulations through peaceful means.
The Fourth Amendment protects individuals from unreasonable searches and seizures by law enforcement. This right ensures that individuals participating in protests are protected from unwarranted intrusion or harassment by authorities. These rights are exhausted during arrest however and law enforcement officials will legally search protesters for their safety.
The Fourteenth Amendment has been interpreted by the courts to require that individuals be treated equally under the law and that discrimination based on certain protected characteristics, such as race, ethnicity, gender, or religion, is prohibited.
Protester Mitigations Techniques for Corporate Security
The increased sophistication of protest groups necessitates a proactive approach by corporate security to crisis management planning. Corporate security managers must be prepared for organized and large-scale protests, understand evolving protester tactics, and develop effective and actionable security plans to counter-protest activity.
Collaborating with local law enforcement, gathering open-source intelligence, monitoring social media, and in some cases, engaging in dialogue with protest organizers through Corporate Communications channels can help mitigate a protest’s negative impact.
As protest groups continue to evolve, it has become crucial for corporations to establish comprehensive security responses to ensure the safety of their personnel, assets, and business reputation. Corporate security responses must include considerations for continuous intelligence gathering, legal considerations, public relations – corporate communications coordination, corporate security limitations, law enforcement response techniques, and the active monitoring of pre-protest indicators.
Effective intelligence gathering is a critical component of the corporate security response to organized protest activity. This involves monitoring and analyzing information related to potential protest groups and protest leadership through publicly available social media platforms, activist group communications, and public announcements of protest activity.
By staying informed about the scheduling, goals, tactics, and potential risks associated with protest activities, corporations can proactively assess and prepare for potential security threats, Protest groups also conduct intelligence gathering, and in most cases, elevate their activities based on historical protests and security responses.
It is not uncommon for protesters to overcome past mitigations by security teams through trial and error and adjust their tactics. Identifying pre-protest indicators through active monitoring of open-source intelligence (OSINT) can help corporations anticipate and prepare for potential protest activity.
These indicators may include online discussion boards, public announcements, historical patterns or anniversaries, and intelligence from credible sources. By monitoring and analyzing these indicators, corporate security teams can assess the level of risk and implement appropriate security countermeasures.
When faced with organized protest activity, corporations must navigate the legal landscape to ensure compliance with applicable laws and regulations. Any legal response must consider the rights and freedoms of protesters, as well as the rights and responsibilities of the corporation.
Engaging corporate legal counsel to provide guidance on permissible security measures, crowd control, and potential liability issues is crucial in creating a balance between protecting corporate interests and the rights of protesters. Corporate legal counsel should also communicate approved legal remedies for those protesters arrested during their activities when they cross the legal threshold for criminal prosecution.
Local police agencies and prosecutors may be hesitant to arrest or even prosecute protesters who violate the law without the support of the victim company. When considering a corporate legal response, companies have three general response options:
Support: Openly support the protest and its cause, especially if it aligns with your company’s values. Support may boost your brand image and employee morale.
Neutrality: Remain neutral and focus on ensuring safety and business continuity. There is always the possibility that any response may embolden protesters and even be misunderstood. Regardless, senior company leadership and legal counsel should approve all protest responses as they may negatively impact the company. If the protest is not directly related to your company, neutrality is often the best choice.
Opposition: Senior Managers may choose to oppose the protest if it goes against your company’s core values. Communicating opposition to a protest group should be carefully considered and done so with sensitivity.
When managing protest activity, in addition to public safety concerns, Corporate Security leaders must also consider corporate management policies centered around:
Public Perception: How the public perceives your company’s actions and stance in relation to the protest heavily influences your reputation, customer loyalty, and investor confidence.
Brand Image: Protests can significantly impact your brand image, either positively or negatively, depending on how you handle the situation. Aligning with public sentiment on social issues can enhance your image while mishandling it can lead to boycotts and possible damage.
Employee Morale: Your employees are also stakeholders. Their perception of your company’s response to protests can affect morale, productivity, and retention.
Media Coverage: Protests often attract media attention. How you respond will be scrutinized and can shape the narrative surrounding your company. All security personnel should understand that their actions and responses when interacting with protesters will be filmed and, in many cases, manipulated by protesters for the benefit of their cause.
Managing public relations and corporate communications during organized protests is essential for maintaining a positive corporate image and brand protection. Effective public relations coordination involves developing messaging that demonstrates respect for freedom of expression while emphasizing the corporation’s commitment to the safety of its employees, customers, and the community. Transparent communication, timely updates, and engagement with stakeholders can help mitigate reputational risks and foster understanding.
Corporate security teams should recognize their limitations when responding to organized protests. While their primary focus is protecting people and assets within the corporate environment, decision-makers may lack the training, resources, and authority to engage with protesters inside or outside their business premises. Pre-incident collaboration with local law enforcement agencies by corporate security leaders is an integral part of the emergency response to organized protest activity.
Establishing clear lines of communication, identifying key stakeholders and decision-makers, sharing intelligence, and coordinating response plans with law enforcement can enhance the effectiveness of security measures. Law enforcement agencies possess the authority and expertise to manage protests, legally enforce laws, and ensure public safety, enabling corporations to focus on protecting their immediate surroundings and personnel.
Corporate and Contract Executive Protection teams should always be included in the security planning and integrated responses to protest activity. Protest activity at speaking events and specifically Heckler responses require unique planning by EP teams and event staffing.
While the specific mission of an EP team is centralized around the protection of a limited number of key corporate leaders, the corporate security response to protest activity should be communicated for effective EP coverage and protectee logistics during protests. In most cases, the target and intended messaging of protest groups is directed at a company’s leadership. EP teams should participate in all planning and fully understand the intended corporate security responses to protest activity to provide situational awareness and operational protective coverage.
Conclusion
Organized protest activities present unique challenges for corporations and corporate security teams, requiring a comprehensive security response that balances the protection of people, assets, and reputation with respect for personal rights and constitutionally guaranteed freedoms.
As protest activity becomes more adaptive and organized, corporate security teams should establish continuity plans, incorporating intelligence gathering, legal considerations, public relations coordination, recognition of corporate security limitations, and collaboration with law enforcement.
With a robust intelligence program and the continued assessment of pre-protest indicators and information, corporations can enhance their ability to effectively respond to organized protest activity while maintaining a secure and productive environment for all stakeholders.